
Tor & onion access
Every public description routes users through Tor Browser toward a v3 .onion. Mirrors exist for uptime; phishing exists for profit—verification is mandatory.
Blackops Onion is the hidden-service string tied to Blackops Market in open-source reporting. This page expands the homepage summary into twelve concrete themes—access, coins, mirrors, escrow, reputation, phishing, and the policy context that surrounds any high-profile darknet brand.
Marketplace taxonomy
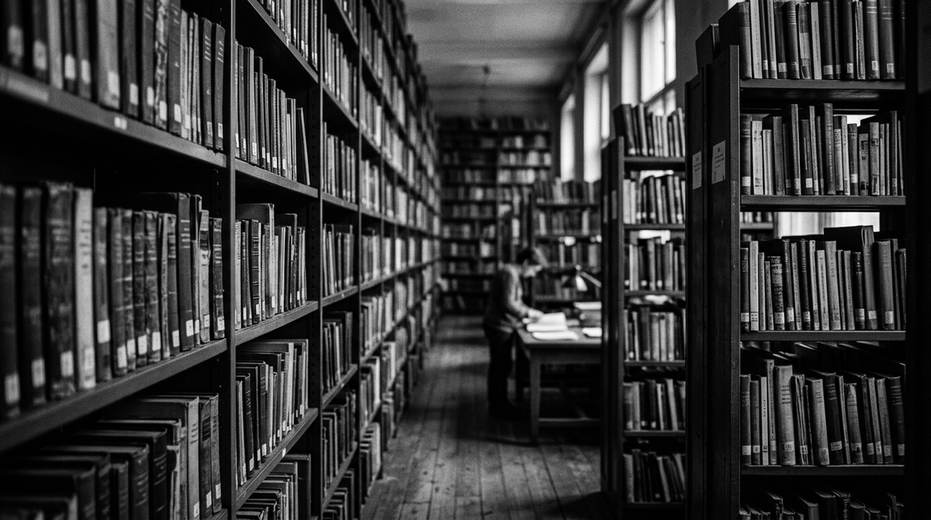
Open sources describe Blackops-style venues using the same listing buckets as other Tor markets: digital goods, physical shipments, services, and reputation-scored vendors. Court exhibits sometimes screenshot category trees as evidence of how storefronts are organized—not as a catalog for readers to replicate.
Forum threads mix product chatter with escrow timers, mirror warnings, and PGP announcements. Researchers treat those patterns as primary-text context; this site does not operate a storefront or queue orders.
Blackops Darknet scrapes may label categories differently than live HTML; normalize names before you compare datasets.
Delivery
Forum posts and indictments mention packaging markers, tracking myths, and customs language. Treat each claim as anecdotal unless you have a primary document. When Blackops Onion appears next to “tracking” keywords in search logs, it usually means someone is trying to confirm a mirror—not asking for postal coaching.
Blackops Url spam that promises “stealth profiles” is marketing noise, not engineering truth.

Every public description routes users through Tor Browser toward a v3 .onion. Mirrors exist for uptime; phishing exists for profit—verification is mandatory.

Open reporting pairs Blackops Market with XMR because stealth addresses complicate naive tracing. BTC sometimes appears for legacy buyers.

Operators publish multiple onions for resilience. Analysts track which mirrors reuse CSS hashes and which diverge—divergence can mean a fake.

Forum threads outline escrow timers, moderator steps, and refund language. Read them as documentation of trust systems, not legal advice.
Feedback scores, dispute counts, and PGP age are debated constantly. Treat reputation as noisy signal unless backed by third-party evidence.

Signed announcements rotate keys on a published schedule. Abrupt key swaps without explanation are treated as compromise rumors in open chatter.

Public guides push checksum verification and cold storage. Wallet malware is a generic infosec problem, not unique to one market name.

Typosquatted Blackops Url hosts appear whenever attention spikes. Bookmark verified strings; ignore DMs that “confirm” new onions.

Indictments and forum posts discuss packaging, tracking folklore, and customs risk at a high level. None of that replaces postal law where you live.
Blackops Darknet boards mix vendor ads, buyer reviews, and staff warnings. They are primary-text sources for researchers, not shopping assistants.

Different jurisdictions define facilitation, possession, and surveillance differently. This page stays descriptive; ask counsel for operational answers.

Public health agencies publish overdose and safer-use material next to market reporting for a reason—use the harm-reduction annex here the same way.
Use this overview the way you would read a dossier: check dates, compare archives, and demand signatures. Blackops Market is a label in public discourse; Blackops Onion is one string inside that discourse—not a magic stamp of safety.
Closing note: keep harm-reduction and phishing tabs open next to market material so readers see emergency and verification resources in the same session.